contact us
Abacus Quality System Services, Inc.
6161 Savoy Drive, Suite 455,
Houston, TX 77036
USA
In today’s current threat environment, it takes a cybersecurity attack from a bad actor to completely derail the operations of a company. Though cybersecurity insurance can cover the costs of a security incident, reputational losses amongst clients and employees can take a very long time to recover from. It is best to avoid these situations completely. If an incident does occur, an effective cybersecurity program will minimize losses and business interruptions.
According to the Cyber Security Annual Report published by NIST based on the study conducted by Check Point Research (CPR), the threat surface of an organization has expanded and there are a lot more ways for a cybercriminal to penetrate the surface. This is especially criticial with the popularity of cloud computing and network-connected smartphones. A once well defined and hardened network perimeter is now blurred and porous to cyberattacks and bad actors are well aware of this.
If there’s one clear takeaway from 2019, it is that no organization is immune from a devastating cyber attack. Cyber exploits are more sophisticated, elusive, and targeted than ever before. With cybercrime rates estimated to have generated $1.5 trillion in 2018 (according to “33 Alarming Cybercrime Statistics You Should Know in 2019” by Casey Cane, Security Boulevard), navigating today’s complex cyber threat landscape requires both a comprehensive cybersecurity solution and a very aggressive posture.
Implementing the NIST Cybersecurity Framework is probably one of the best ways to mitigate the risk of a cyber-attack and protect your data and the network. NIST Cybersecurity Framework consists of 5 functions as shown in the diagram below.
 The Framework is designed to complement existing business and cybersecurity operations. It can serve as the foundation for a new cybersecurity program or a mechanism for improving an existing program. The Framework provides a means of expressing cybersecurity requirements to business partners and customers and can help identify gaps in an organization’s cybersecurity practices.
The Framework is designed to complement existing business and cybersecurity operations. It can serve as the foundation for a new cybersecurity program or a mechanism for improving an existing program. The Framework provides a means of expressing cybersecurity requirements to business partners and customers and can help identify gaps in an organization’s cybersecurity practices.
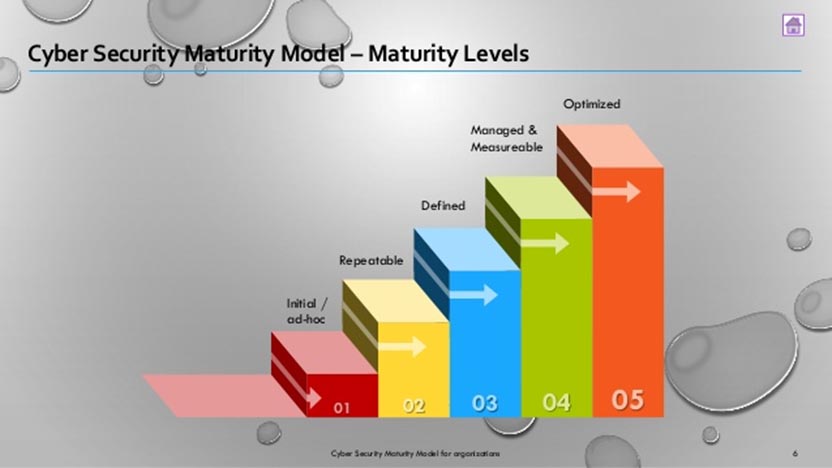
Regardless of what maturity level your cybersecurity program may be, we can help.
We will be happy to give you more information about our services. Please fill in this form to contact us. We will respond as soon as possible.
Abacus Quality System Services, Inc.
6161 Savoy Drive, Suite 455,
Houston, TX 77036
USA